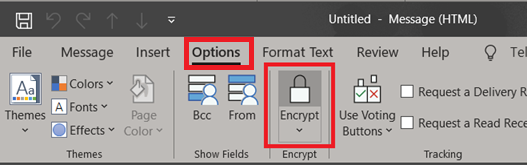
Requirements to use Information Protection (AIP, MIP, RMS) in your organization

Sometimes, when you work with something over time, and then want to explain some of the functionality to others, it is easy to jump some steps. I have gotten some feedback from readers that has made me realize that there are a few things that should be added to many of my posts.