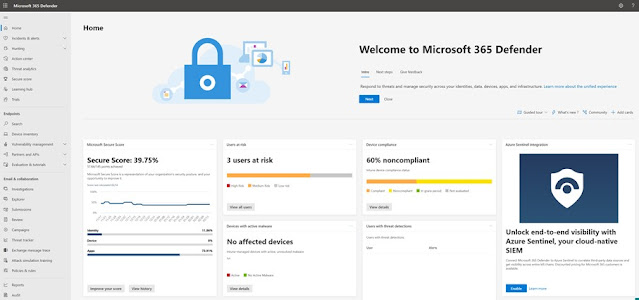
Microsoft 365 Defender – part 3
In our previous posts, we have looked at some of the basics of Microsoft 365 Defender. For those of you who want to learn more, Microsoft has done something pretty amazing for us. They have included a learning hub. Here you can look at different learning paths, look at info for the different products and also go into specific topics. ( Part 1 and part 2 in this series can be found by clicking on the links.) Free training! (Yay) By selecting the Products option, you are able to look at specific products that you want more info about: The different Defender products in Microsoft 365 Defender. If you want to search for a topic, you have quite a few to choose from: Topics But for today we will be looking at another interesting feature in Microsoft 365 Defender, and this is located under Endpoints in the left menu. As you can probably tell, Endpoints is where we find some of the info related to our clients. There are other places as well, but we will get into that later. Here we wil