Things to consider when you want to get started with information protection (MIP/AIP)
Information Protection gives us the opportunity to classify, label, protect and monitor our (sensitive) information. A lot of improvements has happened over the past years, and it is maturing into a solution I feel everyone should care about.
For us who has worked with information protection/RMS for a few years, we always had this feeling that it would one day just explode and become super popular, because how could it not? Who wouldn't want to gain insight into their own data, and have the option to secure what they find most valuable?
And later I saw that we received more and more questions about it, and we did a few implementations here and there, but it never really caught on. Not the way I thought it would anyway. So, I asked myself why. Why didn't people, even those who had invested in E5 licenses, and who could use the full power of Information protection, start with Information Protection? And the answers where many. We will one day, we don't have time, we need to clean up our data first, we haven't moved to the cloud etc. etc. But many also asked me: How should we start? Well, it is not the technical stuff that usually get's people in trouble. It is the lack of planning.
People will have different thoughts on that. How to start, that is. And I am not saying this is the definitive answer, but it is what I do based on my experiences. First you may want to know a little bit about what prerequisites you might have (allthough these, as so much else, changes over time) Requirements to use Information Protection (AIP, MIP, RMS) in your organizatio:
When I began with RMS I thought that it would be enough to have a standard setup with standard protection, and in some ways it can be, but do we adjust our businesses to AIP/MIP, or do we adjust AIP/MIP to fit our businesses? The answer to me is: A little bit of both. I usually always start with a talk. Talking to the customers about how they work with information, who talks to who, what kind of information do they work with, and what levels of sensitivity do they feel they have. In that way we can create a set of classifications which can be used towards MIP.
So what is this onboarding policy? Well it is a way to give MIP to only the users you specify. This way you can do a pilot, or introduce MIP gradually into your organization: AIP Onboarding policy
I also think it is extremely important to have a sensible tooltip that will help your users understand when to use the label. This will be what the users see when they hover over the label in any app:
I usually also implement a couple of easy DLP rules, that can target for instance GDRP data, or Credit Card info for instance: Setup Office 365 DLP rules
You may also need to create a few sensitive information types that fit your scenario: Add new sensitive info types
As you might see, it is easy to get started, and it really doesn't have to be (shouldn't be) too complex, especially in the beginning. A small and easy to understand setup is a great way to get started.
For us who has worked with information protection/RMS for a few years, we always had this feeling that it would one day just explode and become super popular, because how could it not? Who wouldn't want to gain insight into their own data, and have the option to secure what they find most valuable?
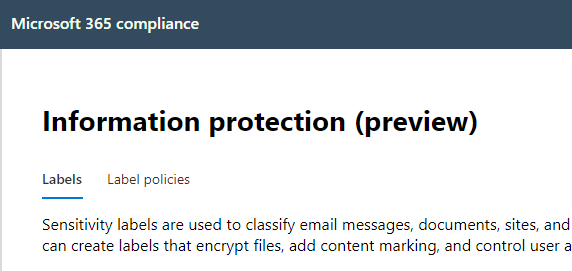 |
| The information protection console in preview |
And later I saw that we received more and more questions about it, and we did a few implementations here and there, but it never really caught on. Not the way I thought it would anyway. So, I asked myself why. Why didn't people, even those who had invested in E5 licenses, and who could use the full power of Information protection, start with Information Protection? And the answers where many. We will one day, we don't have time, we need to clean up our data first, we haven't moved to the cloud etc. etc. But many also asked me: How should we start? Well, it is not the technical stuff that usually get's people in trouble. It is the lack of planning.
People will have different thoughts on that. How to start, that is. And I am not saying this is the definitive answer, but it is what I do based on my experiences. First you may want to know a little bit about what prerequisites you might have (allthough these, as so much else, changes over time) Requirements to use Information Protection (AIP, MIP, RMS) in your organizatio:
When I began with RMS I thought that it would be enough to have a standard setup with standard protection, and in some ways it can be, but do we adjust our businesses to AIP/MIP, or do we adjust AIP/MIP to fit our businesses? The answer to me is: A little bit of both. I usually always start with a talk. Talking to the customers about how they work with information, who talks to who, what kind of information do they work with, and what levels of sensitivity do they feel they have. In that way we can create a set of classifications which can be used towards MIP.
 |
| A few steps to get started. |
I also think it is extremely important to have a sensible tooltip that will help your users understand when to use the label. This will be what the users see when they hover over the label in any app:
 |
| Tooltip |
I usually also implement a couple of easy DLP rules, that can target for instance GDRP data, or Credit Card info for instance: Setup Office 365 DLP rules
You may also need to create a few sensitive information types that fit your scenario: Add new sensitive info types
As you might see, it is easy to get started, and it really doesn't have to be (shouldn't be) too complex, especially in the beginning. A small and easy to understand setup is a great way to get started.



Comments
Post a Comment