Azure Information Protection - Labeling and encryption of information.
A significant part of our work days consist of creating and exchanging information and there’s a big chance that some of that should be secured from prying eyes or competitors. There are several systems that can help us with this, and today we will have a look at Microsoft's solution: Azure Information Protection.
So, what is Azure Information Protection you ask? Good question. If you ask Microsoft, they will say something like AIP is a cloud-based technology that can secure information and give you an overview of where the data is and who has access to it. I will try to tell you a little about what AIP is and why your business should consider implementing it.
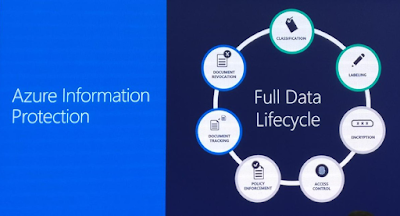
Azure Information Protection is Microsoft's continuation of Azure RMS, which in turn can be said to be a continuation of AD RMS for those of you who have knowledge of that. AIP came about when Microsoft bought Secure Islands. They then merged Secure Islands’ classification and label technology with Azure RMS and went from using Azure RMS as a security product, that encrypted and secured information, to form AIP. AIP uses encryption/security from RMS, and add classification/label technology from Secure Islands to categorize and protect information based on what it contains and how sensitive the content is. Microsoft often uses the following image to show us what AIP is:
When we activate AIP in the Azure portal, two default templates are automatically created (Depends on when you active/activated AIP. Microsoft can and have changed this earlier). They are "Confidential" and "Confidential View Only". These can be used as they are to secure the data but be aware that they only grant rights internally and cannot be used to share outside the organization. With “the same organization” in this case we mean the same Azure tenant. Once the data has been encrypted we can control who has access to them.
If we share a protected file, we can follow it through the Azure RMS portal, see who has opened / tried to open it and at the same time get other information. If we see that something strange happens, for example. that someone tries to access a document from another part of the world than the user usually works/resides we can revoke the access. Depending on the templates we have used to protect the content, document access can be revoked instantly, or over time.
Next time we will look at how we can set up Azure Information Protection in a few simple steps.
 |
| Azure Information Protection |
- Classification: Evaluating the data and decide how sensitive /not sensitive the information is.
- Labeling: "Labeling" of the data based on the classification above. These labels can be linked to RMS templates if we want, and in this way both label and protect the data at the same time.
- Encryption: RMS secures the data based on RMS templates.
- Access Control: AIP ensures access through rights. We grant these rights to email addresses (users or groups) and the recipients must verify their identity.
- Policy Enforcement: The rules the applied to the information, based on the classification / label above, will determine if the data can be read, edited, printed etc. or not accessed at all.
- Document Revocation: If we for instance see suspicious behavior, we can choose to revoke access through the RMS portal. We can also define in advance whether this revocation should take place immediately or not.
When we activate AIP in the Azure portal, two default templates are automatically created (Depends on when you active/activated AIP. Microsoft can and have changed this earlier). They are "Confidential" and "Confidential View Only". These can be used as they are to secure the data but be aware that they only grant rights internally and cannot be used to share outside the organization. With “the same organization” in this case we mean the same Azure tenant. Once the data has been encrypted we can control who has access to them.
If we share a protected file, we can follow it through the Azure RMS portal, see who has opened / tried to open it and at the same time get other information. If we see that something strange happens, for example. that someone tries to access a document from another part of the world than the user usually works/resides we can revoke the access. Depending on the templates we have used to protect the content, document access can be revoked instantly, or over time.
| Azure RMS Portal |
Next time we will look at how we can set up Azure Information Protection in a few simple steps.



Comments
Post a Comment